Most online services have built-in security systems that alert employees when the systems detect “unusual” activity on their accounts.
For example, legitimate email services or similar will send notifications about attempts to reset the phone number and e-mail address linked to the account, or the password.
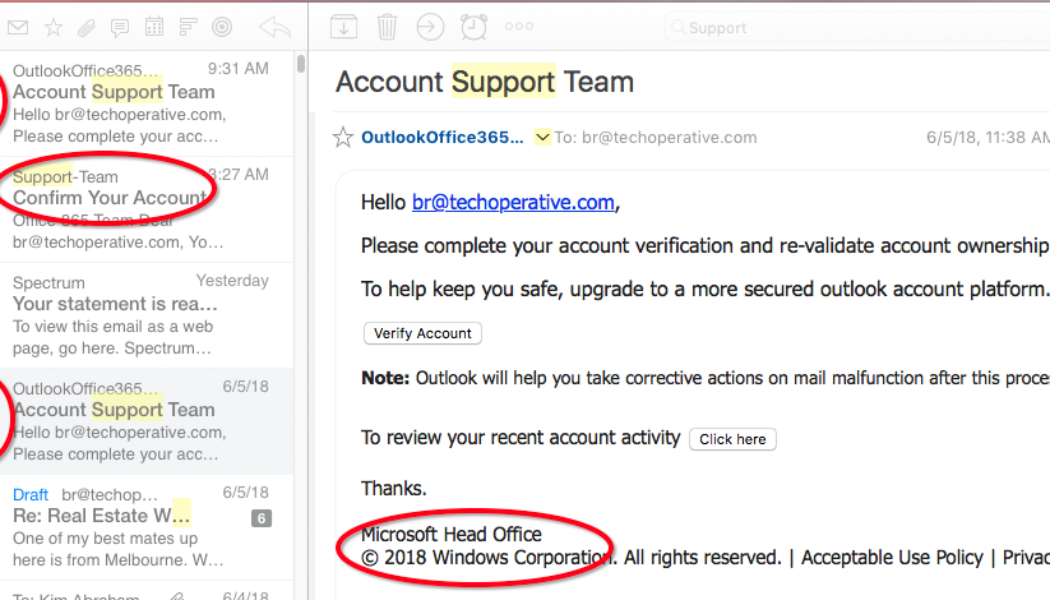
Of course, as soon as such messages became commonplace, enterprising cybercriminals tried to imitate this mechanism to attack corporate users.
As cyberattacks rely on the human factor more often each year, and as cybersecurity technologies progress, such tricks are becoming more and more common and are being registered in multiple mailouts around the world.
The scenario is usually as follows: if it’s a public online service attacker it will usually make every effort to create exact copies of a real message. However, if attackers are hunting for access to an internal system, they often have to use their imagination as they might not know how the email should appear.
Everything about this message looks ridiculous, from the incorrect language to the rather dubious logic — it seems to be at once about linking a new phone number and about sending a password reset code. Nor does the “support” e-mail address lend credibility to the message: there is no plausible reason why a support mailbox should be located on a foreign domain (let alone a Chinese one, for example).
The attackers are hoping that their victim, fearing for the security of their account, will click the red “DON’T SEND CODE” button. Once done, they’re redirected to a website mimicking the account login page, which, as you’d imagine, just steals their password. The hijacked mail account can then be used for BEC-type attacks or as a source of information for further attacks using social engineering.
“Spam and phishing attacks are probably the most underappreciated type of cyberthreats. Even the most responsible employees can be tricked into clicking on them, everyone tends to lose their focus in the hustle of a working day,” says Maria Garnaeva, a cybersecurity expert at Kaspersky.
The good news is modern cybersecurity solutions are often equipped with proper despams filters, and most employees’ training in cybersecurity hygiene is successful at preventing such incidents from occurring,” she says.
What to explain to company employees:
To minimise the chances of cybercriminals getting their hands on employees’ credentials, communicate the following to them:
- Never click on links in automatic security notifications, whether real-looking or not.
- On receiving a notification, check the security settings and linked details, do so by opening the website in the browser manually.
- A clumsily worded notification (as in the example) is best ignored and deleted.
- If the notification looks real, notify the IS service or security officer; it may be a sign of a targeted attack.
Edited by Zintle Nkohla
Follow Zintle Nkohla on Twitter
Follow IT News Africa on Twitter










Tagged: BEC-type attacks, Clone accounts, Cyber criminals, cyberattacks, cybersecurity, cybersecurity technologies, Email Phishing Attacks, Email Scams, Foreign domain emails, Internal System, IT, IT News, Kaspersky, Mailouts around the world, Online attackers, Online Attacks, Online service attackers, Password reset code, phishing attacks, Security, Security Online, tech news, technology