Pretend, for a moment, that you are the president. This ransomware thing is escalating. Like, hackers screwed with the gas supply on the East Coast — nightmare! You’re going to have to make some policy decisions to make these attacks end because that’s the scale of the thing.
Let’s begin with the obvious, uncontested fact: the number of ransomware attacks is going up because companies are paying the ransoms.
The Colonial Pipeline hack is a case in point. The company spent $4.3 million to unlock its computers. Ransomware is just extortion, after all. As the DarkSide collective put it in their weirdly corporate apology for shutting down Colonial Pipeline, “Our goal is to make money.” Major cybercrime gang Evil Corp — great branding btw — reportedly likes sick Lambos. Stopping ransomware is simple in that way: all you have to do is cut off the cash.
The question is how, and none of the choices are very good.
You could require the immediate disclosure of ransoms. You could ban paying ransoms outright. You could ban cryptocurrency, which is how most ransoms are paid. You could increase regulation around cryptocurrency and perhaps ban certain kinds of exchanges or transactions. You could try being better friends with Vladimir Putin, in the hopes that he might sacrifice some threat actors. Your Department of Defense has also probably come up with some separate terrible ideas, which I am frightened even to contemplate.
Every choice here hurts, at least in the short term. But let’s go through them.
Immediate disclosure of ransom payments
Legislators have been trying to get ransom disclosures done already, without much success. That’s probably because the public disclosure of a hack damages a company’s reputation. So right now, we actually don’t know the true extent of the ransomware problem because a lot of companies keep hacks quiet.
Immediate disclosure would at least give us a better sense of what’s going on, but there would be a cost: hackers would get more leverage. Like, hackers create leverage now by making a hack’s existence public, which creates pressure on the company to get things back to normal — by paying up. Cybercriminals create leverage in uglier ways, too: emailing and calling employees or clients of the victim company to tell them about the hack, says Ali Arateh, managing director of Mandiant, a cybersecurity firm.
In early June, security researcher Kevin Beaumont tweeted that he’d send out a thread of the biggest ransomware and extortion victims — then he decided against it since some of the hacks weren’t public. “And there goes my hopes for the leverage,” tweeted back Mannus Gott, one of the ransomware groups in question, which had evidently been hoping for a public disclosure of their hack in order to better pressure the victim. “Yours was one I was looking at, at the time,” Beaumont replied.
Ban ransom payments
Right now, it is legal to pay ransom: it’s even tax-deductible, and the money often comes from a company’s cyber insurer. Banning ransoms in the US would cut off the cash supply for the criminals — probably getting them to change their focus to other countries.
This policy is in place already, in a piecemeal way. The leaders of Evil Corp were criminally sanctioned to prevent people from paying them ransom, not because Russia would extradite them. Similarly, the North Korean nationals behind the Sony hack are beyond the US’s reach, though I’m sure law enforcement would be happy to pick them up if they took a vacation in a country with a US extradition treaty. If a company pays a sanctioned actor — or a sanctioned crypto wallet — it can put itself in legal jeopardy. But some still pay! About 15 percent of all ransomware payments, or about $50 million in cryptocurrency, were subject to sanctions liability, according to Chainalysis.
This piecemeal ban is also part of the reason we’ve seen the rise of affiliates — a banned actor like Evil Corp can sell its software product to a group that isn’t sanctioned in return for a cut of the ransom. That group then carries out the hack and demands ransom, and the company pays a non-sanctioned wallet. It’s ransomware-as-a-service.
Still, making all ransom payments illegal could cut down the number of companies that hand over their money. Right now, about 1 in 4 companies that receive ransom demands actually pay, according to security firm Sophos. “In the long term, stopping ransom would probably halt this, but in the short term it would be very painful,” says Tom Robinson, the founder and chief scientific officer of Elliptic, a company that tracks cryptocurrency transactions.
It would be painful for the same reason that companies often pay the ransom: they might go out of business otherwise. Many hackers deliberately target companies’ backups, says Joshua Motta, co-founder and CEO of Coalition, a cyber insurer. If the company’s backups aren’t segmented away from the rest of the network, they may be vulnerable, he says. “It’s devastating,” he says.
And as if that weren’t enough, a lot of hacks double-dip — they steal data as well as encrypting systems. The data can then be sold for other attacks if the ransom isn’t paid, and it may include such sensitive information as Social Security numbers lifted from payroll data.
It might also increase cyber insurance underwriting costs, though this is debatable. According to the Sophos survey, paying the ransom actually makes hacks more expensive because companies still have to do some pretty serious work to fix their systems and lock them down on top of paying the ransom money. It’s unclear whether that would still be true if more companies have no choice but to rebuild their computer systems from scratch.
Ban cryptocurrency
Cryptocurrency’s role in the ransomware ecosystem has led some to call for banning cryptocurrency altogether. Others have suggested regulating cryptocurrency mining as money transmitters to make it more difficult to process ransom transactions. “I think it’s time for a whole-of-government ‘regulate it to death’ strategy, based on existing regulation,” says Nicholas Weaver, a computer security specialist at the International Computer Science Institute in Berkeley, California, in an email. This would also be a painful route to take — not only would it blow up people’s cryptocurrency investments, but it would nuke entire companies based on cryptocurrency, such as Coinbase.
It’s also not clear that banning cryptocurrency would work; most cryptocurrency is decentralized. Banning it within US borders would remove a lot of the more above-board players who are currently compliant with know-your-customer measures, while the shadier exchanges based outside the US would continue operating.
But ransomware as we know it is heavily dependent on cryptocurrency. Ransom demands in traditional currency require banks or payment processors to be involved in the process, and they can intervene to halt payment. This was functionally what ended “screen lockers,” which demanded a credit card payment to unlock the victim’s computer, according to Ryan Olson, the VP of threat intelligence at Palo Alto Networks’ Unit 42. Crypto doesn’t have the same oversight, and it also makes it easier to quickly move money across borders.
Right now, ransom payments are usually made in Bitcoin, though Samantha Levine, senior vice president at CAC Specialty’s cyber practice, tells me she’s also seen payments made in Ethereum and even Dogecoin.
There is one silver lining to cryptocurrency as a ransomware payment method: public blockchains make cryptocurrency traceable. Some cryptocurrencies, called privacy coins, are harder to track. For instance, the DarkSide group responsible for the Colonial Pipeline hack also would have accepted ransom in Monero, a privacy coin, but Monero doesn’t change hands as often as Bitcoin. That makes it difficult for companies to quickly acquire Monero to pay ransom. Instead, Colonial Pipeline paid 75 Bitcoin, or about $4.3 million. The FBI followed the transactions through the public blockchain to seize and recover $2.3 million in funds.
If cryptocurrency is banned outright, a lot of the privacy initiatives in that world may suddenly get a lot more important. For instance, there are services called mixers that let people move their identified cryptocurrency to mingle with other transactions of roughly the same amount of money, ideally obfuscating the transaction history. Right now, most cryptocurrency players don’t use them — but if cryptocurrency becomes illegal, their use may very well rise. Ethereum creator Vitalik Buterin has even suggested creating a mixer on the Ethereum chain.
Another way to obscure transactions is to use a privacy wallet, such as Wasabi, with built-in capabilities to make transactions hard to follow. Driving all cryptocurrency use to these kinds of wallets would make it even more difficult to trace ransom payments.
Stronger cryptocurrency regulation
At some point, criminals need to move out of cryptocurrency and back into traditional currency since that’s generally how one pays for Lamborghinis. Within the borders of the US, cryptocurrency is already regulated; reputable exchanges comply with know-your-customer laws aimed at preventing money laundering, for instance.
But not every exchange is based in the US, and some aren’t engaging in strict know-your-customer practices. More money associated with criminals went through the Binance exchange than any other, according to Chainalysis. Now the US government is investigating it for money laundering.
While ransomware players can be anywhere in the world, there are a few places where they cluster. DarkSide, the group that was responsible for the Colonial Pipeline, “doesn’t eat in Russia,” Brett Callow, an analyst at Emsisoft, told the Financial Times. Its ransomware software “checks the language used by the system and, if it’s Russian, it quits without encrypting.”
One way to dodge exchanges altogether is to make arrangements on darknet markets, such as Hydra. Someone might, for instance, bury rubles in a specific location — and then, when the threat actors hand over their bitcoin, they receive the coordinates to go dig the fiat currency up, says Robinson. But it’s hard to see what people are doing on Hydra — it’s also possible that some cybercriminals might buy tools they can then use in other attacks, effectively reinvesting in their business.
International diplomacy and coordination
You could combat ransomware through international cooperation — after all, many hackers’ names and locations are known. They’re just not extraditable. But because hackers don’t target certain Eastern Bloc countries, those countries do not view ransomware as a serious problem, says Adam Meyers, Crowdstrike’s senior vice president of intelligence. “These people are paying taxes,” Meyers says. “I think there’s people protecting them.”
The Biden / Putin summit on June 16th underscores this difficulty. One of the outcomes of that meeting was to create meetings of cybersecurity experts who might decide certain kinds of infrastructure is “off-limits” to attacks, according to The Washington Post. But this is not the same thing as banning ransomware outright, or being able to pursue hackers, like those of Evil Corp, within Russia.
In order to do that, it’s possible Putin will ask for significant concessions, such as lifting some US-imposed sanctions or otherwise making deals that benefit Russia.
Well?
So where does that leave you, the president? Nowhere good. But you’re going to have to put on your decision aviators because the hacks are increasing. Even cyber insurers can fall prey to ransomware. Cyber insurer CNA was hacked in March and paid a ransom of $40 million. The Asia division of cyber insurer Axa was hacked in May.
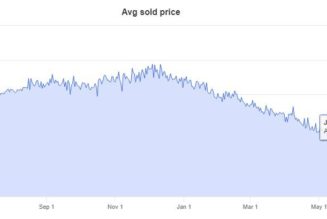
“We called 2020 the year of ransomware, and I’m wondering if I have to call 2021 the year of ransomware, too,” says Kim Grauer, director of research at Chainalysis. “We’re basically on track to surpass 2020.”
The trends she’s seen include asks for bigger ransoms and an increase in the average payments going to known ransomware wallets. And scarily, there’s more money being moved between ransomware strains and illicit service providers, says Grauer. Business is good, and the hackers are reinvesting.